Forensics
Background
Background
By now, you might ask yourself if all of these claims about The Deck can be verified.
Yes they can!
But to prove everything for yourself you need some technical background. After an overview of this background, I will describe how to verify and date the existence and provenance of these NFTs. If you are already well versed in online and cryptographic forensics, then you may skip ahead.
Blockchain Forensics
![]()
The Breakout Chain blockchain contains all information needed to verify the existence and provenance of The Deck NFTs, but since Breakout is a relatively unknown chain, I will focus below on alternative forensic analysis drawing from information on the internet. This forensic analysis will rely only on a couple of authoritative record keepers: The Internet Archive (a.k.a. The Wayback Machine) and VirusTotal.
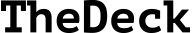
As a prelude, however, I will point out that it is simple to determine the existence and provenance of The Deck NFTs using a Breakout Chain block explorer. Just head over to explorer.breakoutcoin.com and type in the upper case symbol for any card in the search field and it will tell you the card’s ownership and any transactions. For example, the ticker symbol for the Ace of Spades is DAS (for “Deck Ace of Spades”), and it will take you to the DAS explorer page. As one can see on that page, DAS was created on June 11, 2016 and has had three owners. Links to these explorer pages are also in the Gallery.
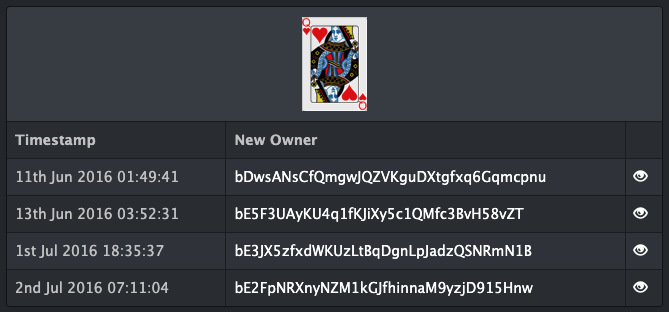
Screenshot of the DAS explorer page. The owner addresses are listed in chronological order. Clicking the icon on the right of the owner table will give details about the transaction that gave the address ownership.

The Internet Archive
The Internet Archive’s Wayback Machine is an online resource that stores snapshots of web pages dating back to 1996. Archived pages are presented as they appeared on the date of the snapshot. The snapshot date is also displayed at the top of the page.
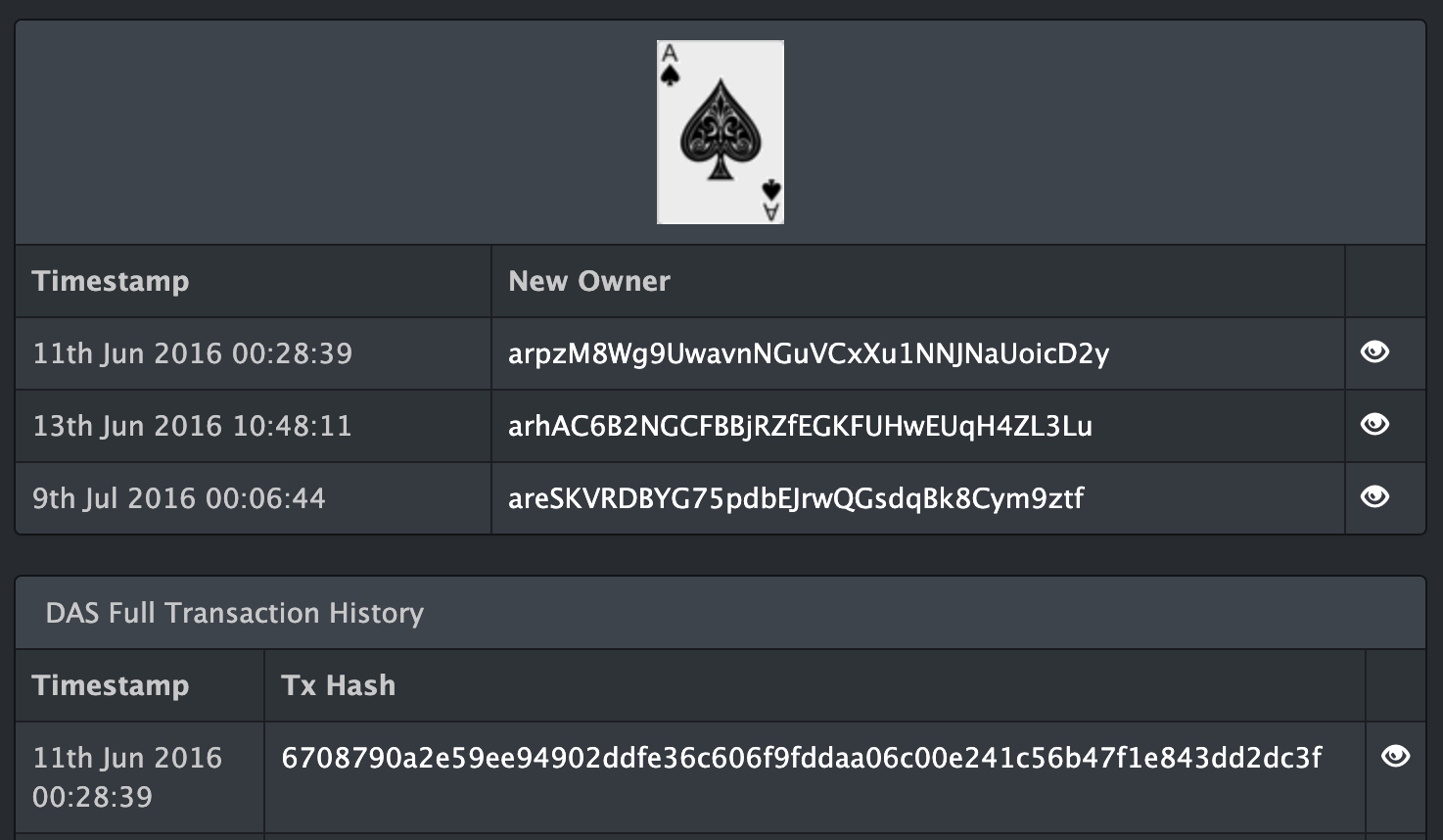
Screenshot of the Wayback Machine’s archive of the Breakout block crawler on July 4, 2016. Although a block hash isn’t shown, other information that unambiguously identifies the chain is present, including the mining difficulty to 12 digits.
VirusTotal
The forensics herein relies heavily on VirusTotal, a website where users can manually check single files for viruses using dozens of different anti-virus services.
Several years ago, the typical wallet software for cryptocurrency users was an application known as a “reference client”. The reference client was the software for the cryptocurrency itself. Many cryptocurrencies, like Breakout Chain, also had a built-in GUI (graphical user interface) wallet where users could send and receive transactions with a few clicks.
To use a GUI wallet, users would have to run the client and wait for it to download the complete blockchain. This process was called “syncing the blockchain”. Such a setup may seem unreasonably cumbersome for users today, but this was typical for the time, which is considered to be early times for cryptocurrencies.
Image of the Bitcoin GUI client called “Bitcoin Core”. This type of client was often referred to as “the Qt” because it was created using the Qt application framework. Several images of Breakout Chain’s Qt are shown elsewhere.
At the time, cryptocurrency developers built wallets as distributable apps for desktops (OS X/macOS and Windows). Of course these desktop wallets were sometimes created by malefactors to be vectors for malware. To ease the minds of users, and to ensure safe builds, developers such as myself made a habit of submitting their distributable apps for Windows and OSX to VirusTotal, which gave a comprehensive analysis of any potential malware.
Proof of Existence
When VirusTotal checks a file, it identifies the file by a cryptographic fingerprint known as the SHA256 hash. Incidentally, this is the same cryptographic fingerprinting function (with slight modifications) used by bitcoin for identifying blocks and transactions. I won’t go deeply into the technical details of hash functions here except to say that every file will have a different SHA256 hash with astronomical certainty. In other words, we can be certain that no two files (pieces of data) will have the same SHA256 hash. This certainty is the bedrock of billions of dollars of digital transfers every day, as well as numerous other applications absolutely essential to modern civilization.
An important feature of cryptographic fingerprints is that a particular cryptographic fingerprint represents all of the data used as an input to the fingerprinting function. For example, imagine we digitize the entire Library of Congress and then make an SHA256 hash of that digital information. Later, if we want to recreate that hash, we will need every bit of data that went into it when the hash was first calculated. If even one bit of data is added, omitted, or changed then the fingerprint will be entirely and unpredictably different. If we publish this fingerprint somewhere, then this publication serves as virtually irrefutable “proof of existence” for the data that went into it.
A shorter and more technically accurate term for “cryptographic fingerprint” is “cryptographic hash”. Cryptographic hashes have a widely used property in that they can be combined with other data, and then the combination itself can be hashed, creating a new fingerprint. This “chain of hashes” is used in several places in cryptocurrencies. For example in coins like Bitcoin, the data for each block of a blockchain includes the cryptographic hash of the previous block, called a “block hash”. In this way, the block hash is a proof of existence (PoE) for ALL preceding blocks back to the first block, called the “genesis block”. Since a block includes data for all its component transactions, then a given block hash represents every prior transaction stored on the blockchain.
This feature of cryptographic hashes is of paramount utility, because to publish proof that some information exists, one doesn’t need to make the entire body of information available, only the 64 characters (32 bytes) of the cryptographic hash. This short representation makes these proofs of existence easy to publish.
VirusTotal will only scan a file once, unless a user explicitly requests a second check. To recall previous results, the VirusTotal website calculates a file’s SHA256 hash within the web browser. If the file has been scanned before, VirusTotal will present the results of previous scans. These results include not only results of the malware detection algorithms but also other information, most notably the date of the first scan.
The forensics below rely heavily on VirusTotal’s PoE functionality. Importantly, users can verify the earliest known existence of the files and software I discuss herein by dragging them to VirusTotal themselves.
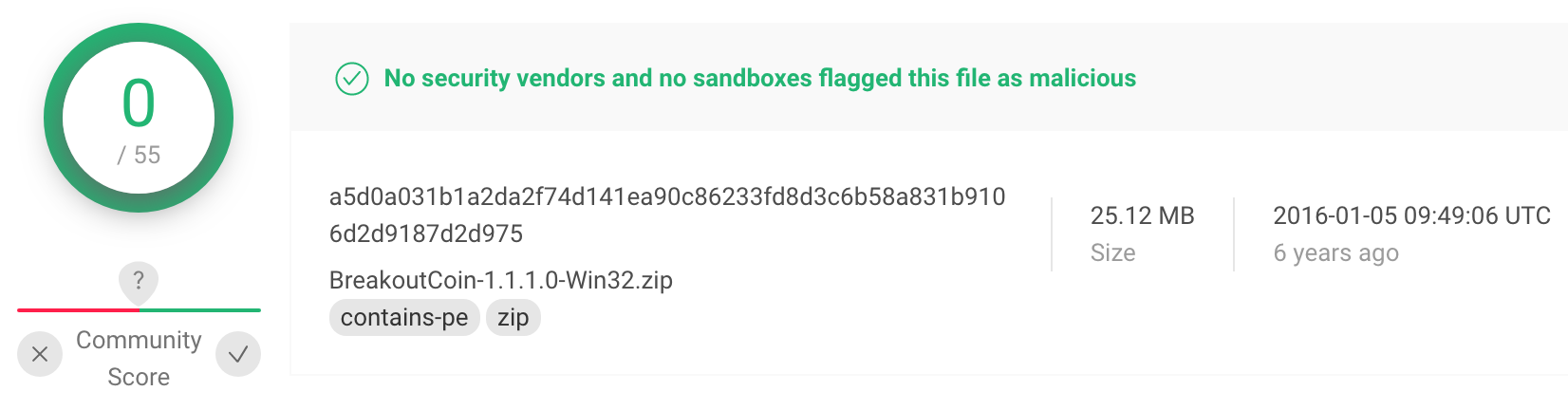
Header for the VirusTotal scan of the Windows version 1.1.1.0 of the Breakout Chain software used in testnet. These VirusTotal results prove cryptographically that this exact version of the software existed on May 1, 2016.
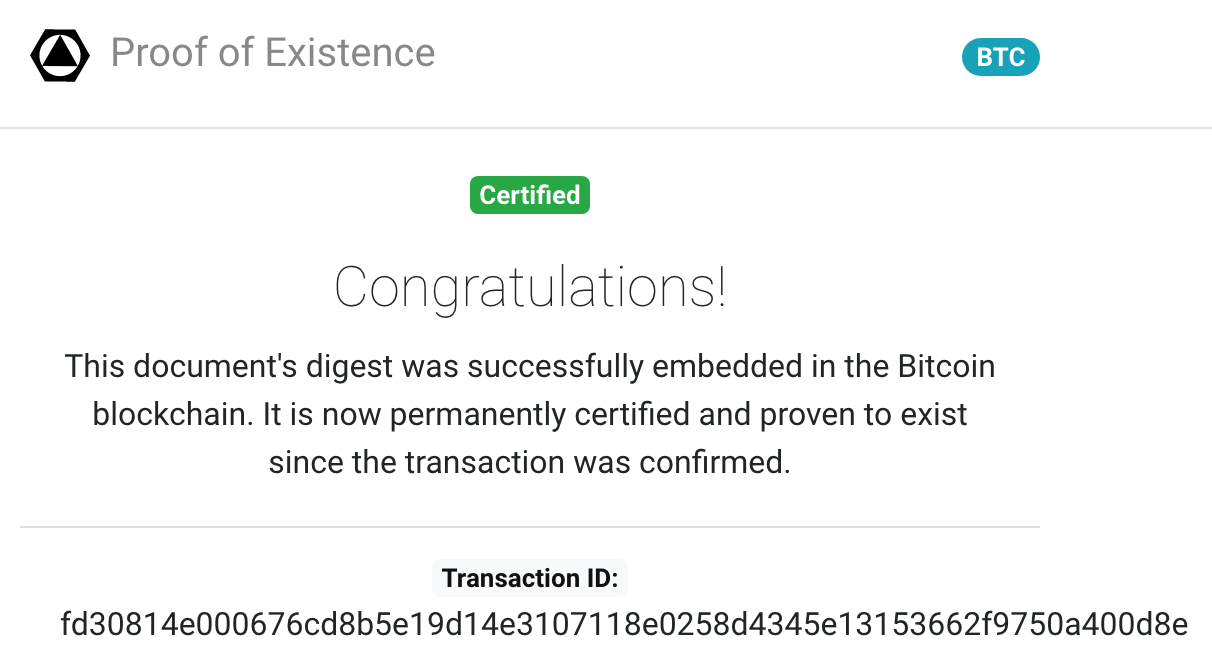
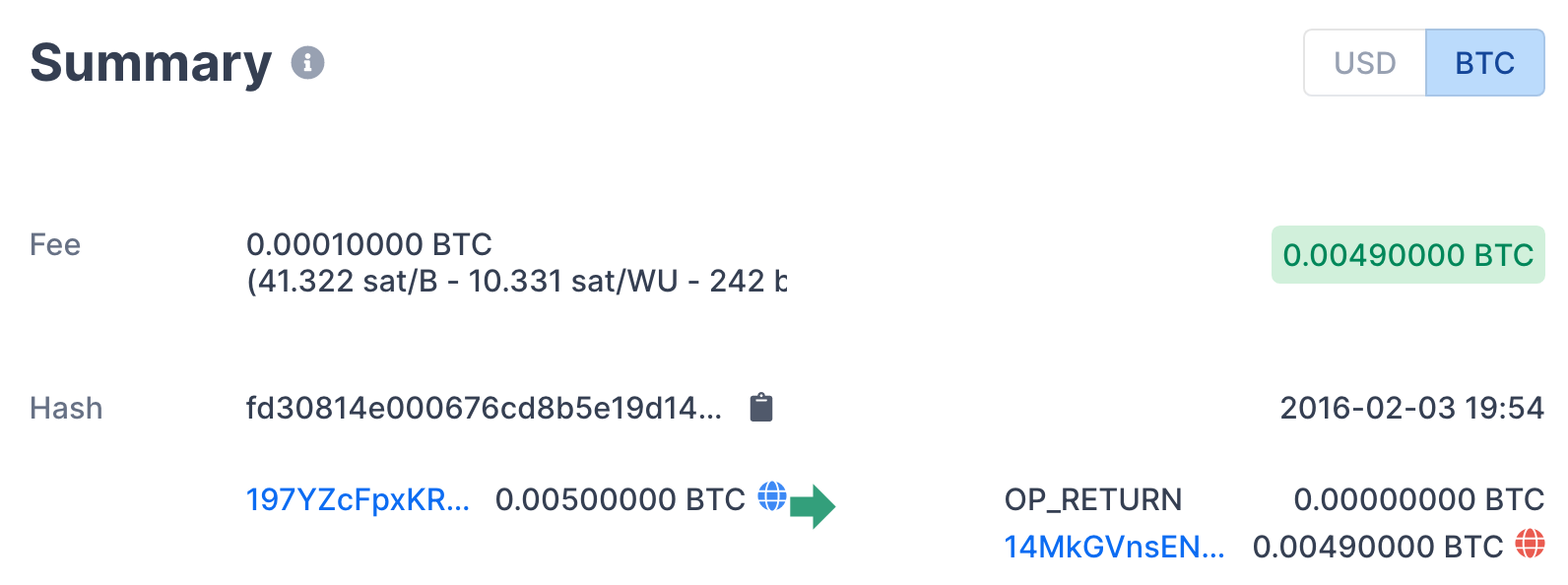
Another resource for cryptographic PoE is the website proofofexistence.com. This website allows a user to drag a file to the homepage, the SHA256 hash is calculated therein, similarly to VirusTotal. The user is presented with a Bitcoin address and an amount to pay. Upon receipt, the hash will be included in the Bitcoin blockchain, creating a PoE for the file.
This process is very similar to VirusTotal, except the hash is stored on the Bitcoin blockchain instead of VirusTotal’s servers. Both Bitcoin and VirusTotal are excellent ways to prove the existence of some information prior to some time.
Header from proofofexistence.com confirming the existence of a document. The PoE shown proves the existence (Feb 4, 2016) of a file that describes in detail the fair lottery used to distribute cards from The Deck to their first owners.
Header from blockchain.info detailing the PoE transaction referenced in the preceding image. In 2016 when this PoE was created, the fee of 0.0049 BTC was about $1.32. At Bitcoin’s all time high, this amount of BTC was worth over $300!
Relevant Forensic Technology
In this section, I describe some simple forensic technology used in the verification of The Deck as a revolutionary NFT project. This section is for hardcore NFT forensic archaeologists committed to fully vetting NFT projects.
Several instructions for verification utilize Linux/Unix commands. If you want to perform these verifications, then you may want to use one of the following: (a) the macOS Terminal program, (b) a Linux box, cygwin (Windows), (c) MSYS (Windows), or (d) a virtual machine (VM) of a Linux box running in VirtualBox (open source) or similar. The commands I provide assume Linux.
One important command that differs between Linux and a stock macOS install calculates the SHA256 cryptographic hash.
For Linux, this command is sha256sum.
For macOS, it is shasum -a 256.
To make macOS behave like Linux, simply add the following command to your shell startup script (“.profile”) and restart the Terminal:
alias sha256sum="/usr/bin/shasum -a 256"
Another command is dd, which is used to extract specific stretches of bytes from any file. This command is basically the same for both macOS and Linux. This command is probably best understood by example:
dd if=BreakoutCoin.exe ibs=1 skip=12309842 count=5433 > DAS.png
In this command, the input file is “BreakoutCoin.exe”. The file skips to byte 12,309,842, reads 5,433 bytes, and then sends them to a new file called “DAS.png”. If you use that on the “BreakoutCoin.exe” from the uncompressed zip file “BreakoutCoin-1.2.4.2-Win32.zip” (link to download), then the new file “DAS.png” will be a PNG image of the Ace of Spades as it is stored in “BreakoutCoin.exe”.

The Ace of Spades as it is stored in the Windows executable file “BreakoutCoin.exe” from the Multicurrency platform version 1.2.4.2 release. Note that the background is transparent, so the card’s appearance will vary depending on background.
In this dd example command, we used a shell redirect (“>”) to send the bytes to a new file called “DAS.png”. We will use this redirect elsewhere in the forensic analysis to create a file containing a hash. The command we will use is:
sha256sum breakout-testnet-sources-564C361B.tar > sources.sha
This command stores the hash of a tar file archive of the Multicurrency version 1.0.1.0 sources into a new file called “sources.sha”, which can be used with proofofexistence.com.

Forensic Landmarks of The Deck
From the description of forensic tools like the Wayback Machine and VirusTotal, it should be obvious that the main goal of forensics is to establish a dated proof-of-existence for The Deck as a set of NFTs. Additionally these forensics should unambiguously establish the early provenance of cards from The Deck. Finally, the forensics should establish clear links between these NFTs, their identities and properties, and their visual representations.
1. September 3, 2015: I start the moderated Multicurrencies whitepaper thread on bitcointalk with an overview of the multicurrency technologies that would enable The Deck.
2. November 18, 2015: Testnet phase 1 for the Multicurrency platform is live, with version 1.0.1.0 reference client builds available.
3. November 18, 2015: A proof-of-existence for the version 1.0.1.0 source bundle is committed to the Bitcoin block chain.
4. January 5, 2016: Testnet phase 2 for the Multicurrency platform is live, with version 1.1.1.0 reference client builds available.
5. January 8, 2016: In a bitcointalk post, I describe the lottery that will distribute the bulk of The Deck NFTs both in testnet and mainnet. In this post I show a preview of the deck for the first time in a screencap of the wallet. This post is historical in that it describes the intent of the Deck as an NFT project, verifiably dated by the Wayback Machine.
6. January 12, 2016: I set up and publicized a rudimentary block crawler for the Multicurrency phase 2 testnet. Several snapshots of the block crawler were archived by the Wayback Machine, providing strong evidence of the early provenance of Deck NFTs from testnet.
7. January 30, 2016: Final testnet version (1.2.4.2) of the Multicurrency platform is released as client builds.
8. February 2, 2016: I published in a bitcointalk post the lottery entrant public keys and the first draft of the lottery script that will be used to distribute the bulk of the cards from The Deck.
9. February 3, 2016: I published in a bitcointalk post a final draft of the lottery script along with its proof-of-existence transaction identifier.
10. February 6, 2016: Bitcoin block 396963 becomes known, providing the seed for the lottery script. I published the lottery winners from the final version of the script, which differs from the PoE version by a single public key that had to be changed at the last minute. This change did not affect the results of the lottery for the rest of the winners.
11. February 6, 2016: History witnesses the world’s first NFT flex.
12. June 10, 2016: The Wayback Machine first archives a description of The Deck at breakoutcoin.com. Note that you must wait for this page to load on the Wayback Machine, and then scroll down.
13. June 12, 2016: Breakout Chain, which hosts The Deck, officially launches to the public with version 1.3.2.0.
14. June 13, 2016: The Deck is distributed on mainnet according to the lottery.
15. June 13, 2016: History witnesses the world’s first NFT flex on mainnet. Unfortunately the image from that flex has since been deleted from its hosted location.
16. November 22, 2016: Breakout Chain version v1.4.5.0 is released with reference client builds for OS X, Raspbian, and Windows. This release has a checkpoint block hash embedded into it and also has a historical scan by VirusTotal dated January 25, 2017, providing a proof-of-existence for the full early provenance of most of The Deck, including those distributed by lottery.
Early Testnet
The Multicurrency platform was the testing ground for what would become Breakout Chain. This platform had two testnet phases. The first phase meant to work the worst bugs out of multi-currencies, in an environment with only two tokens: the “principal” and the “stake”, described at https://breakoutcoin.com/multicurrencies/, which has a link to the whitepaper.
To ensure I could claim this intellectual territory, I took the source bundle for version 1.0.1.0 (the first released version) and committed it to the Bitcoin block chain as a proof-of-existence. Out of paranoia, I didn’t actually submit the bundle to the proofofexistence.com, but a file containing the SHA256 hash of the bundle. So, to validate the existence of these sources on November 18, 2015, do the following steps:
- Download the version 1.0.1.0 source tar file.
- Find the downloaded tar file, named “breakout-testnet-sources-564C361B.tar”, in your shell.
- Issue the following command in your shell:
sha256sum breakout-testnet-sources-564C361B.tar > sources.sha - Open https://proofofexistence.com/ in your browser.
- Find the above created file “sources.sha” in your file explorer.
- Drag the “sources.sha” file onto the proofofexistence.com window in your browser.
Under the word “Congratulations!” on the resulting page, click on “BLOCKCHAIN” to take you to the bitcoin transaction (November 18, 2015) that stores the proof.
The Deck in Testnet
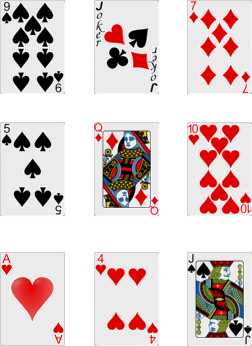
The first appearance of The Deck in the Multicurrency testnet was in version 1.1.1.0, which launched phase 2 of the testnet. To verify and date the presence of The Deck NFT images, follow these instructions:
- Download the version 1.1.1.0 Windows installation bundle.
- Drag the downloaded bundle to virustotal.com to see a proof-of-existence on January 5, 2016.
- Find this downloaded bundle, named “BreakoutCoin-1.1.1.0-Win32.zip”, in your file explorer.
- Double click it, or equivalent, to “unzip” it.
- Find the unzipped bundle, named “BreakoutCoin-1.1.1.0-Win32”, in your shell program, and enter that directory.
- Extract the Ace of Spades with the command
dd if=BreakoutCoin.exe ibs=1 skip=11461721 count=5433 > DAS.png - Open that file by navigating to it with your file explorer and double clicking it.
It is possible to extract not only the Ace of Spades this way, but every other card from the deck. The offsets (“skip” parameter of dd) and lengths (“count” parameter) are at github [link]. Spotcheck a few random cards to convince yourself that all the NFT images are stored in that file and were associated with The Deck NFTs as early as January of 2016!
The Deck Lottery
Most cards of The Deck were distributed using a provably fair lottery. Because bitcointalk threads could get overrun by trolls, especially unmoderated threads, The Deck lottery was organized mostly via Slack, which is similar to Discord. The first mention of The Deck lotteries was on January 5, 2016.
As described elsewhere, in a provably fair lottery it is necessary to commit a proof-of-existence of all aspects of the lottery except for the seed for the lottery’s pseudo-random number generator (pRNG). The seed is necessarily revealed after the commitment from an “incorruptible” source. An example of an incorruptible source is a block hash of the bitcoin block chain. It should be noted that the block number from which the hash would be taken is also part of the proof-of-existence commitment. This block number should be in the future relative to the proof-of-existence commitment.
To verify the existence of the lottery prior to the existence of its seed, follow these instructions:
- Download the lottery in raw format, and save it as “deck-lottery-placeholder.py”.
- Locate “deck-lottery-placeholder.py” in your desktop file explorer.
- Open proofofexistence.com in a browser.
- Drag “deck-lottery-placeholder.py” into the proofofexistence.com window.
- Under “Congratulations!”, click “BLOCKCHAIN” to see the transaction containing the proof of existence, dated February 4, 2016.
- Go to block 396963 in the blockchain.com explorer and see that the date is February 6, 2016.
- If you know how to run a python2 script, copy “deck-lottery-placeholder.py” to “deck-lottery.py” and plug the blockhash for block 396963 into the appropriate place in “deck-lottery.py” and run the lottery to see which public keys get which cards. Note how they match the results on bitcointalk.
- If you have access to a running Breakout Chain client, pick a public key and note its card. Execute the following command with the public key with the client, matching the public key and expected card, in the following way:
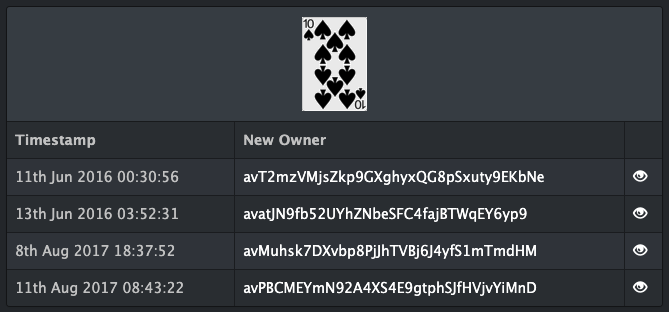
validatepubkey 03f445047839579f8d3bc173706364a67f9eb80aa9c88dcab6bf75aa8af65677e1 DTS - Take the address given (in this case avatJN9fb52UYhZNbeSFC4fajBTWqEY6yp9) and plug it into the search bar at explorer.breakoutcoin.com.
- Verify that the address was the second owner of the card.
Ownership history of the Ten of Spades (DTS) according to explorer.breakoutcoin.com. Note that the second owner is avatJN9fb52UYhZNbeSFC4fajBTWqEY6yp9. Cards were mined into existence then distributed according to the lottery, so lottery winners were the second owners, not the first.
Feel free to spotcheck any lottery winner to see that the ownership matches the lottery results both on bitcointalk and by running the lottery script (modified with the correct seed) for which there was a proof-of-existence. The one exception is the Queen of Hearts (DQH), which was distributed to bE5F3UAyKU4q1fKJiXy5c1QMfc3BvH58vZT instead of bDy9H4UNFJ5CRLYoe5e5oVJhpvvxoK5md3o at the request of the winner. The final lottery script, with this change and the seed from block 396963, is linked here.
Ownership history of the Queen of Hearts (DQH), which was distributed to a different address from that committed to in the lottery’s proof-of-existence.
Provenance of the Deck in Testnet
Business considerations related to the Breakout project resulted in a long gap between achieving a fully functioning Multicurrency testnet and finally launching the Multicurrency platform on the Breakout Chain mainnet. For this reason, The Deck on testnet preceded The Deck on mainnet by nearly half a year, making the testnet NFTs significantly earlier than the mainnet NFTs. Fortunately, a cryptographic commitment to the provenance of the testnet cards can be found on the Wayback Machine.
This commitment takes the form of a 20 byte (160 bit) SHA1 hash found in the page source of a June 12, 2018 archive of the testnet release repository. SHA1 is used by git to assure the integrity of code repositories. In short, the entire contents of the repository, as well as all revisions, go into the SHA1 hash. If one byte of the repository or its history is changed, added, or removed, the SHA1 hash will differ.
On November 20, 2015 I set up the testnet release repository to hold both distributable reference clients and bootstrap files that embody the data of the entire growing testnet blockchain. These bootstrap files for the Multicurrency testnet record the complete provenance of all the testnet NFTs. As a result, the git SHA1 hash is a cryptographic proof-of-existence of this provenance.
To verify all of the bootstrap files at the testnet release repository, follow these instructions.
- Go to the most recent commit of the testnet release repository [link].
- Note the commit hash is 96833fa42a41222888b8e52e923b022437bb0250.
- Go to the June 12, 2018 Wayback Machine archive of the testnet release repository [link].
- Show page source in your browser. In chrome and other browsers, one typically right-clicks inside a blank area of the page, and selects “View Page Source”. This does vary by browser.
Search for the string “96833fa42a41222888b8e52e923b022437bb0250” to verify it is embedded in the page source.
This process demonstrates a cryptographic proof-of-existence for the provenance of the testnet NFTs as early as June 12, 2018, albeit the testnet started in January 2016.
The Deck in Mainnet
Of course the Deck appears in mainnet, but a hard core NFT archaeologist may want to verify and date the earliest associations between image and NFT. The Deck first appeared in mainnet with Breakout Chain version v1.3.2.0.
To verify and date the presence of The Deck NFT images on mainnet, follow these instructions:
- Download the version v1.3.2.0 Windows installation bundle.
- Drag the downloaded bundle to virustotal.com to see a proof-of-existence on July 3, 2016.
- Find this downloaded bundle, named “BreakoutCoin-1.3.2.0-Win32.zip”, in your file explorer.
- Double click it, or equivalent, to “unzip” it.
- Find the unzipped bundle, named “BreakoutCoin-1.3.2.0-Win32”, in your shell program, and enter that directory.
- Extract the Ace of Spades with the command
dd if=Breakout-Coin.exe ibs=1 skip=13788147 count=5433 > DAS.png - Open the file “DAS.png” by navigating to it with your file explorer and double clicking it.
As with the testnet, It is possible to extract not only the Ace of Spades this way, but every other card from the deck. The offsets and lengths are at github [link]. Spotcheck a few random cards to convince yourself that all the NFT images are stored in that file and were associated with The Deck NFTs as early as July of 2016.
Early Provenance of the Deck in Mainnet
The early provenance of The Deck in mainnet can be verified unambiguously through a SHA256 commitment to the Breakout Chain with the following leading block hash:
0x62d199c756a0f19a0fc1f9e895190b29cb7b7683d284bfcabacbe906df530ff9
This block can be seen at the Breakout Chain explorer here.
To verify a proof-of-existence of this block hash as early as January 25, 2017, follow these steps:
- Download the version v1.4.5.0 Windows installation bundle.
- Drag the downloaded bundle to virustotal.com to see a proof-of-existence on January 25, 2017.
- Find this downloaded bundle, named “BreakoutChain-1.4.5.0-Win32.zip”, in your file explorer.
- Double click it, or equivalent, to “unzip” it.
- Find the unzipped bundle, named “BreakoutChain-1.4.5.0-Win32”, in your shell program, and enter that directory.
- Extract and print the hash of block 13,300 with the command (offset found here)
echo `dd if=BreakoutCoin.exe ibs=1 skip=8954864 count=66`
Check that the last line matches the following block hash:
0x62d199c756a0f19a0fc1f9e895190b29cb7b7683d284bfcabacbe906df530ff9
Because the hash of a block commits to the entire chain preceding it, this hash also commits to the creation and transfers of all NFTs of The Deck prior to that block. Block 13,300 was minted on August 19, 2016, which commits to all of the early provenance of The Deck on mainnet.
Proof of Flex
The first NFT flexes in history were flexes of NFT cards from The Deck. As described in the outline above, the very first was the testnet Jack of Spades on February 6, 2016. This flex is verifiable. History’s first flex on mainnet was of the Nine of Spades June 13, 2016, although the screencap of the wallet is now unavailable. This flex is verifiable, although the image is missing now. The second flex on mainnet is of the Jack of Diamonds on June 13, 2016. This flex is verifiable, and the image is still available.
To verify these flexes, see the following pages on the Wayback Machine, and view source to search the encoded image URLs. Each encoded URL is shown, with a link to the original image. Once you load the linked Wayback Machine page, the search string is the encoded URL.
- First NFT flex [link], encoded image URL:
http%3A%2F%2Fi.imgur.com%2FBgbh6RE.png - Second NFT flex on mainnet [link], encoded image URL:
https%3A%2F%2Fi.imgur.com%2F0IMbTfK.jpg
The decoded URL is used as the link in these two proofs.
Because bitcointalk doesn’t allow robots, the presence of Wayback Machine archives requires a manual request for archival. We are fortunate that the very first flex was archived as far back as February 2016, and that the screenshot of the wallet has never been deleted.
© Copyright 2026 The Deck